EVENT GUYZ
OUR FANS
Don't wait
Let Us Help You
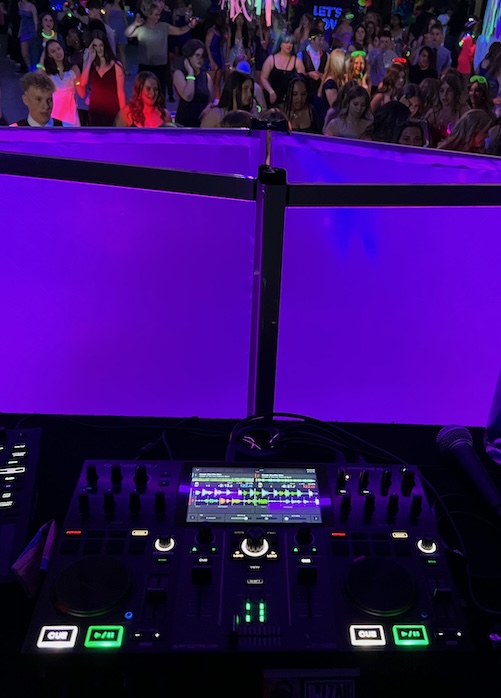
DJ ZAh
Making Good Memories
With Good Music

Our Holy Church
Non-Denominational Church
Here For You When You Need Us

Event Management
Offering a Wide Range
Of Services to Help Manage Your Event
Music
Sound for CHARITY
EventGuyZ gives as much as we can for those that need some help.

Parties
No matter what kind of party it is, we have provided music at them.

Karaoke
When you want a singing party we can provide some karaoke songs for your party.

Weddings
Working with you we make sure you have a great experience.

School Dances
We have a large digital music library that is radio edited and safe for schools.

BAR DJ
Need a DJ to fill in at your bar? We can be that DJ and help provide the music to help you.
RELIGION
WEDDING MINISTER
Rev.Dennis works to customize your wedding for you so its not the same ceremony everyone gets.
BLESSINGS
Do you have an event and would like to have a minister give a blessing before the event? Rev. Dennis would love to help you.
COUNSELING
Need a friend to talk to? Do you want Rev. Dennis visit someone in the hosptial or care center?
Funeral Minister
Let Rev. Dennis help you through this difficult time and help you put together the funeral.
CUSTOMERS
Here are some
of our more large
Happy Customers
Mid-America Festivals / Relay for Life / Davison Middle School
News & Updates
Bouquet Toss
Anniversary Dance
DJ Frequently Asked Questions
Group Dance Songs
Some Great Club Songs
Country Wedding Songs
Ask us anything
EventGuyZ is an LLC that is registered with the state. We focus on doing what it takes to make your event successful.


















